What is Secure Data Destruction?
Secure data destruction refers to the process of permanently destroying data in a way that it cannot be recovered or accessed again. This is typically done to protect sensitive information, whether financial, customer, business-critical or personal data, from falling into the wrong hands or to ensure compliance with laws and regulations regarding the handling of personal or confidential data.
Types of Data Destruction services
There are three main ways to destroy data or to go about hard drive destruction: 1) degaussing, 2) physical destruction, and 3) data overwrite. Each one has its own characteristics and implications.
- Hard drive degaussing
The degaussing method uses high-powered magnets to disrupt the magnetic fields of the hardware’s drive, destroying the data it contains in the process. This method requires the use of specialized equipment, and therefore is usually carried out only by organizations that specialize in data destruction.
- Physical destruction
This straightforward process simply involves tearing apart the hard drive with the use of tools, destroying the information it contains. As the name implies, physical destruction also renders the equipment useless for future use.
- Overwriting
Finally, overwriting data has the benefit of not damaging the hard drive, meaning it can be reused in the future. The process of overwriting involves substituting the information contained in the drive with new data, which gets rid of the content we seek to delete.
Why is it important to destroy data securely?
Failing to destroy sensitive data securely might result in others still having access to it and using it for purposes that can range from industrial espionage to fraud and other malicious activities.
How to securely destroy hard drives
For those who want to accomplish the physical destruction of a hard drive by themselves, the quickest way of doing it involves the following steps: 1) locating the hard drive in question and removing it from the hardware that contained it 2) dismantling the drive with the use of tools such as a Torx screwdriver to open its case and a flathead screwdriver to pry it open and finally 3) removing its board and breaking it.
After these steps, the pieces can be recycled for future use, which is important not just for reducing the environmental impact of IT but also to comply with regulation that aims to limit e-waste and to improve a company’s sustainability scores.
How do you destroy confidential data?
As we’ve established, it’s important to destroy data to ensure it cannot be recovered for malicious purposes, and it’s also important to ensure that the hardware is subsequently recycled or directly reused to avoid the creation of additional e-waste.
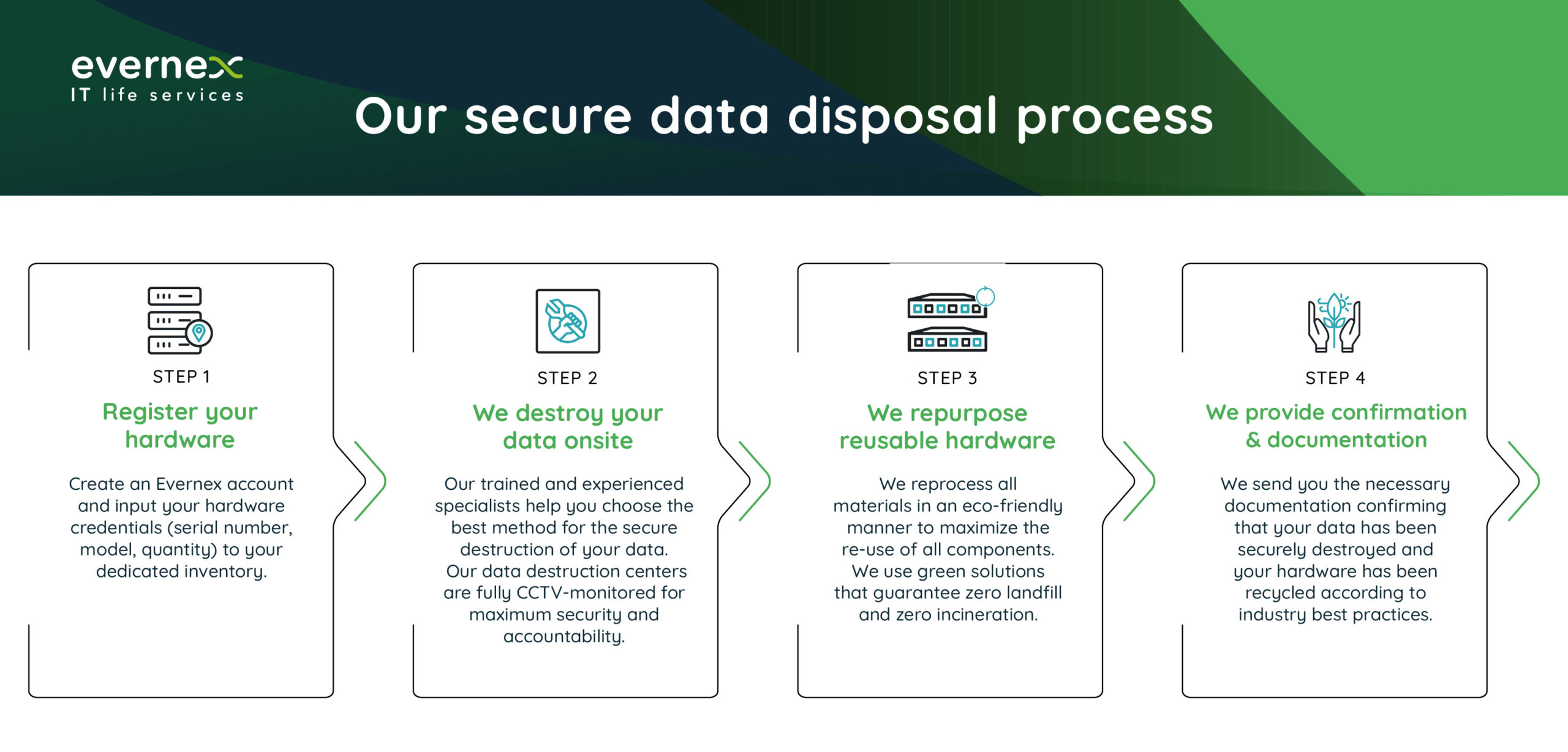
For most companies, the wisest way to proceed once the need for data destruction has been determined is by contacting a business that specializes in this practice. A data destruction service provider, such as Evernex, will not only take care of the process safely and securely, but will also provide guarantees and handle the recycling part as well. Such companies typically carry out the process in a dedicated processing facility.
Things to consider before destroying data
Being organized is paramount when it comes to keeping track of the data we have and what needs to be erased. For this reason, it’s advisable to develop and document a data destruction process outlining the steps needed to carry out the process. This data disposal policy will ensure secure data destruction is carried out consistently and in compliance with all existing regulations. Again, companies that specialize in data destruction can be of great help when it comes to organizing the process and can provide security guarantees.
If you would like more information about how to proceed to achieve safe and secure data destruction for your company, get in touch with our team. Our experts will be glad to handle your questions and requests as well as to advise you on the solutions that best fit your needs.




